What is Trivy?
Trivy is a multifunctional, open-source security scanner. It can scan various targets (filesystems, containers, git repositories and more) in order to discover security issues (vulnerabilities, misconfigurations, and secrets). In short, Trivy can find a bunch of different types of security issue in pretty much anything you point it at, for free.
Scanning AWS
As of this week, Trivy v0.31.0 allows you to scan AWS accounts for security issues. You can either run the CLI locally or integrate it into your CI/CD pipeline.
The rules applied to AWS are all the misconfiguration rules built into Trivy for IaC scanning. This means the rules are consistent across platforms and, as a bonus, can be used to find the causes of AWS issues when infrastructure is defined with Terraform or CloudFormation.
Whilst you can already scan the infrastructure-as-code that defines your AWS resources with trivy config, you can now scan your live AWS account(s) directly too.
Getting Started
Trivy uses the same authentication methods as the AWS CLI to configure and authenticate your access to the AWS platform. This means if you already use the AWS CLI, you should be able to run Trivy against your AWS account without any extra configuration - just point and shoot! Otherwise, you’ll need to configure Trivy to use your AWS credentials.
We recommend you use a user/role with the ReadOnlyAccess policy attached.
Kicking off a scan is as simple as:
1
trivy aws --region us-east-1
You can even omit the --region flag if you have a default region configured in your AWS environment vars or config file.
Reviewing Results
Once the scan is complete, you’ll get an overview in your terminal which should look like this:
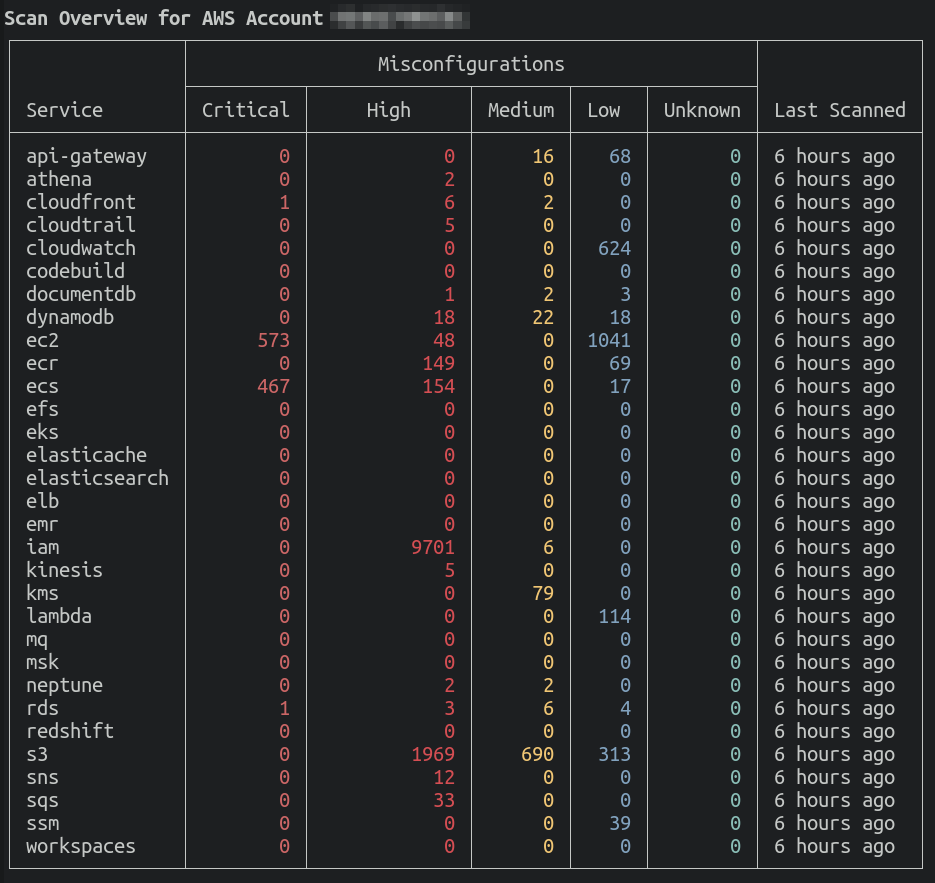
This summarises the number of results - by severity - for each AWS service scanned.
You can run additional commands to filter the results without having to run the entire scan again - results are cached locally per AWS account/region.
To “zoom in” on results for a particular service, you can use the --service flag:
1
trivy aws --region us-east-1 --service s3
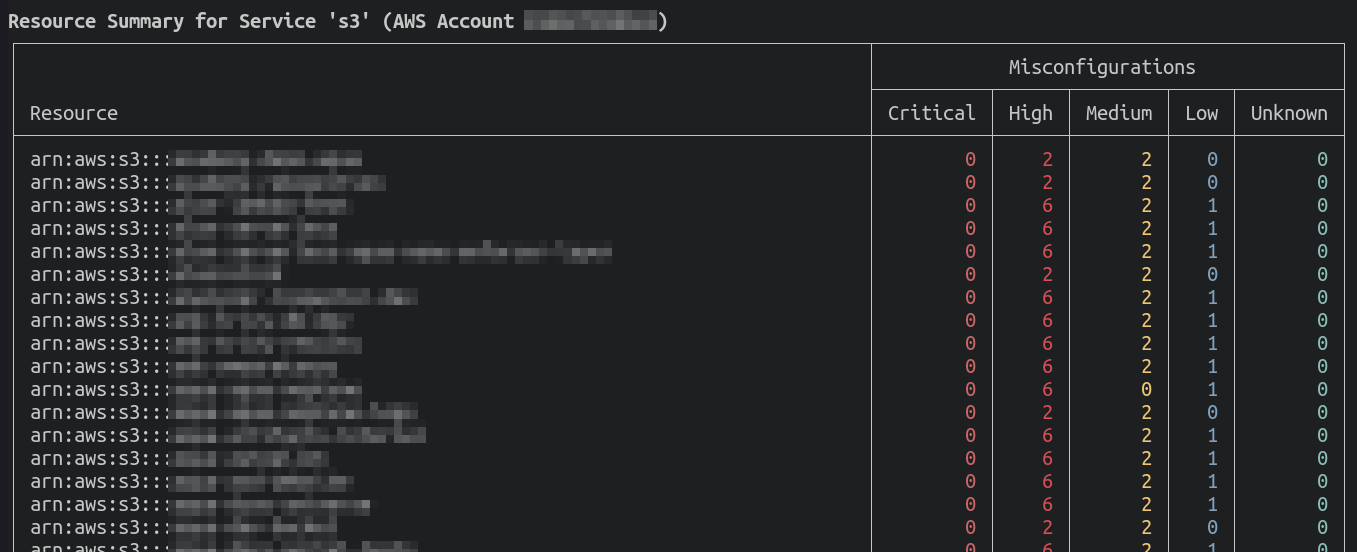
This will give you a summary of the selected service, with the number of issues - again by severity - for each resource within the service. Note that only resources with detected security issues are shown here.
Here’s an example:
You can show the individual issues for a resource by using the --arn flag, for example:
1
trivy aws --service s3 --arn arn:aws:s3:::example-bucket
This will result in output like the following:
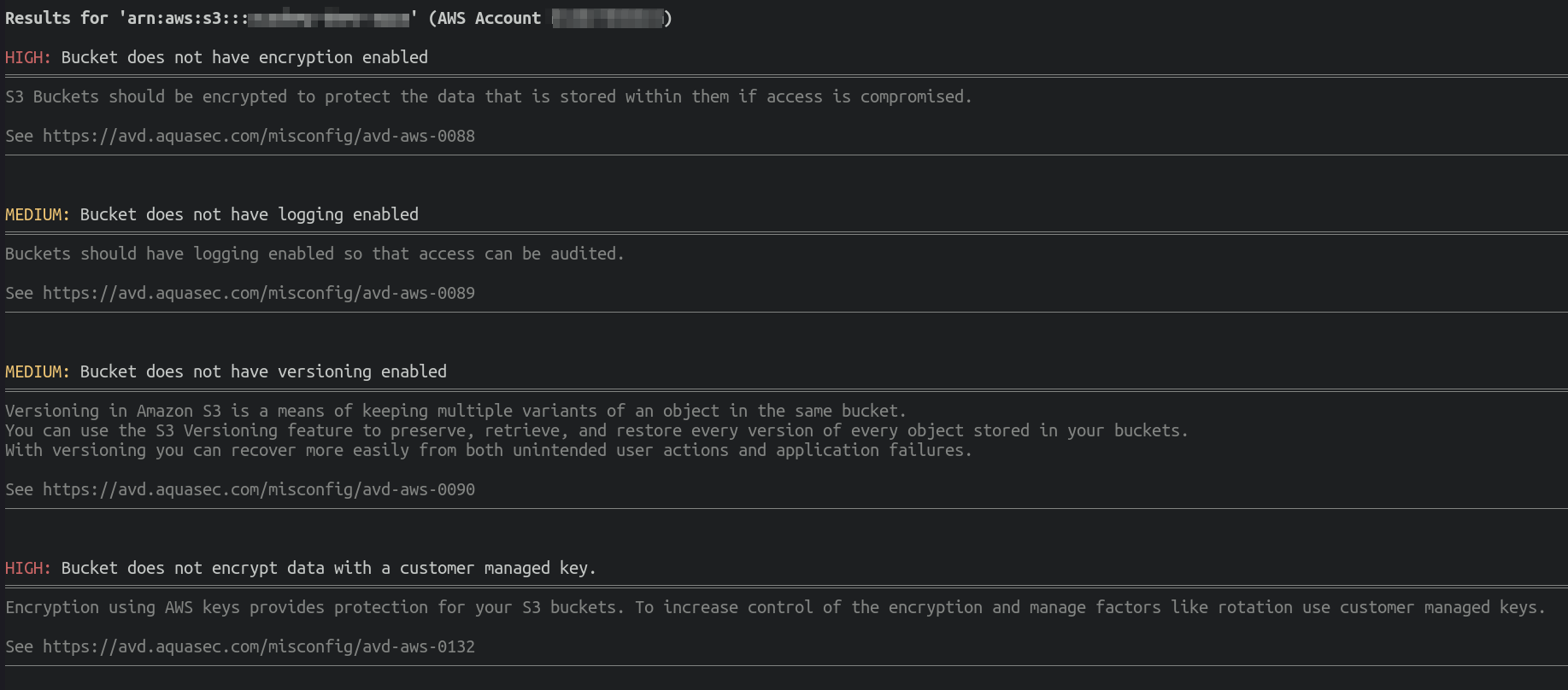
Each result contains a severity, a summary, and further information on the issue, with a link to the relevant AVD documentation which includes various guides on resolving the problem.
Summary
In summary, Trivy can now scan AWS accounts for security issues, with all the capabilities of its existing community-enhanced misconfiguration checks.
Join the Trivy community
We have lots of exciting plans for Trivy. Become part of the journey by joining our Slack community and contributing on GitHub. Also, let us know if you have questions or if there are other features you’d like to see in Trivy.
And when you try the new Trivy features, share it on social media! 🙌
Comments powered by Disqus.